
In the world of Web3, where decentralization and trustlessness reign supreme, traditional security models simply don't cut it. Instead, we rely on a powerful combination of cryptography and economic incentives – a system known as crypto-economic security.
Let's explore how this innovative approach safeguards decentralized networks and applications.
Understanding Crypto-Economic Security
Crypto-economic security is the backbone of decentralized networks. It's a system where economic incentives and cryptographic techniques work in harmony to ensure network security. Unlike traditional systems that rely on central authorities, Web3 applications leverage cryptographic proofs and economic game theory to guide participant behavior and achieve network goals.
This means that the participants are incentivized to act honestly because it's more costly to cheat than to cooperate.
Simple, effective, and crucial for keeping decentralized systems trustless.
But why do security incentives matter?
Decentralization, by its very nature, eliminates central control — that means no firewalls or corporate admins. This makes economic incentives important to reduce network vulnerability to various attacks, such as Sybil attacks, collusion, or double-spending.
Here are a few ways to encourage participants to be a good actor:
- Follow consensus rules (e.g., Proof-of-Stake validators staking funds that they lose if they act maliciously).
- Execute smart contract operations correctly (e.g., keepers ensuring timely and accurate execution of automated tasks).
- Secure network transactions (e.g., miners and validators receiving rewards for securing blockchain networks).
Incentives create an environment where participants naturally choose the honest path—not because they have to, but because it’s the best move financially.
Enforcing Good Behavior in Web3 Task Execution
So now the question arises - how do decentralized networks ensure that tasks are executed correctly?
Well, there are a few well designed well-designed crypto-economic mechanisms like:
Staking & Slashing
Most of the networks require participants to stake a predefined amount of tokens before they participate. This is called Staking.
If any participant fails to perform their duties or act maliciously, they can lose these staked tokens. This is what is called Slashing.
This is standard in Proof-of-Stake (PoS) networks and in keeper networks like TriggerX, where keepers must stake tokens to be eligible for automated task execution.
Game-Theoretic Incentives
By designing incentives that reward honest behavior, networks encourage participants to follow the rules. For instance, in TriggerX's keeper network, keepers are rewarded for correctly executing tasks and penalized for mistakes or malicious actions.
Reputation-Based Systems
Networks also utilize reputation systems for enforcing good behaviour. This is as simple as participants building their credibility by being consistently honest and by doing so unlocking bigger rewards and responsibilities.
Dishonest actors are gradually phased out over time from the network.
Collateralization and Bonding
In high-stakes environments, actors must put up collateral before performing key tasks. If they misbehave, that collateral is seized, making fraud an expensive mistake.
Crypto-Economic Security vs. Traditional Security
Crypto-economic security flips the traditional security model on its head. Here’s how they compare:
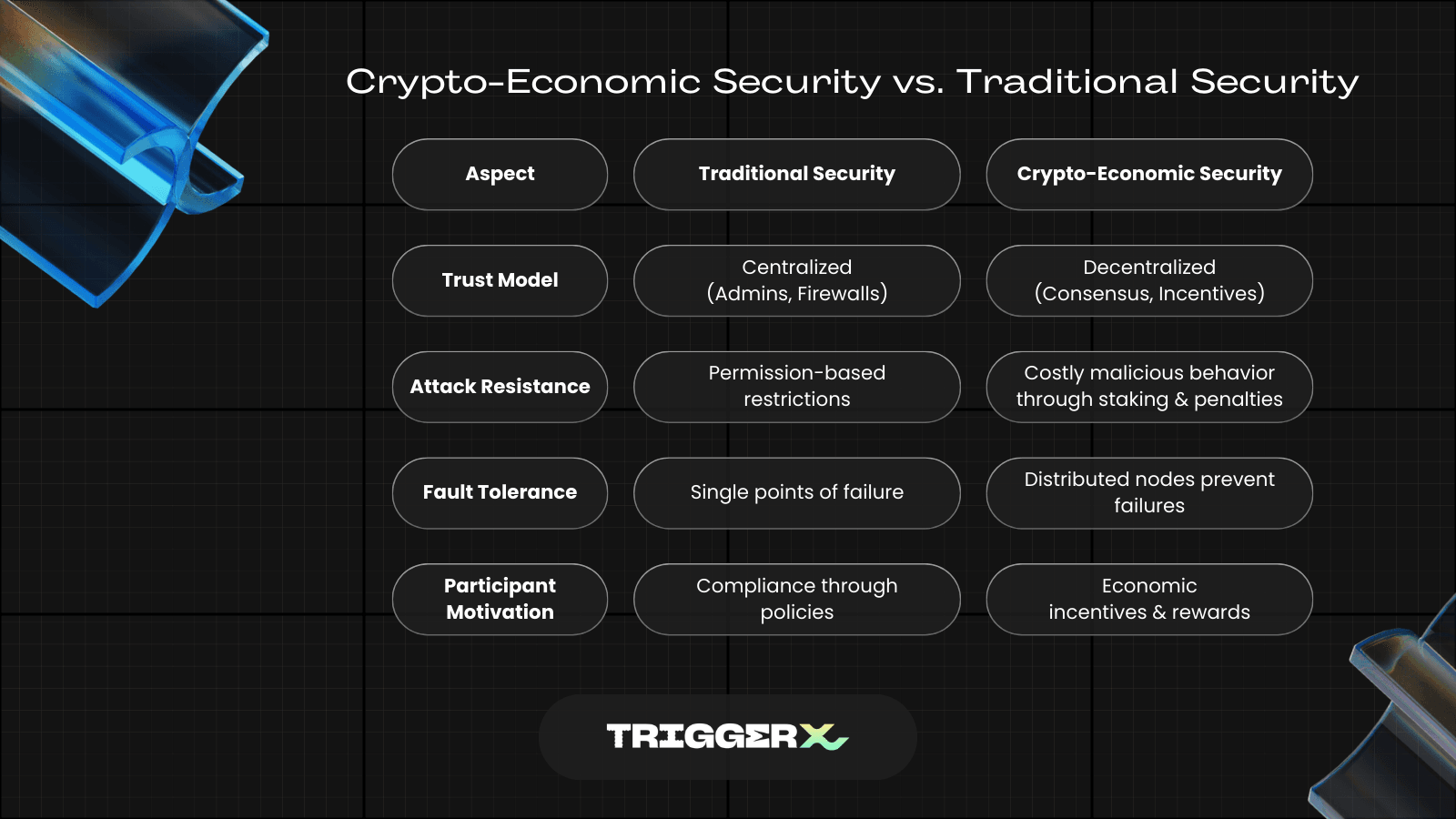
Instead of securing systems through firewalls and permissions, crypto-economic security makes dishonest actions costly, removing the need for centralized control.
Real-World Use Cases: Where Crypto-Currency Works
Crypto-economic security isn’t just theoretical—it’s already powering some of the biggest innovations in Web3. Here’s where it plays a crucial role:
DeFi Platforms
Lending: Borrowers must over-collateralize loans to prevent defaults.
Liquidity Pools: Users provide liquidity to earn rewards, keeping decentralized exchanges functional.
Platforms: Aave, Compound, Uniswap
Keeper Networks & Automation
Keeper networks like TriggerX automate tasks such as liquidations and rebalancing.
Keepers earn rewards for completing tasks correctly and face penalties for dishonesty.
This removes the need for intermediaries and ensures transactions execute smoothly.
Decentralized Storage
Storage providers stake tokens as a security deposit. If they lose or tamper with user data, they lose their stake—making dishonesty unprofitable.
Oracles & Data Feeds
Oracles provide real-world data to smart contracts. Malicious oracles face financial penalties, ensuring accurate data delivery.
Platforms: Chainlink, Pyth Network
Rollups & Layer 2 Networks
Fraud proofs and optimistic rollups use economic incentives to ensure off-chain transactions are valid. Invalid transactions result in lost bonds, making fraud costly.
The Future
Crypto-economic security is what makes decentralized applications actually decentralized. By combining cryptographic methods with carefully designed economic incentives, Web3 networks become resilient, efficient, and self-sustaining.
For projects like TriggerX, robust crypto-economic security ensures that keepers execute tasks diligently and discourage dishonest behavior by making it financially costly. As Web3 evolves, crypto-economic security will remain a cornerstone of trustless, decentralized systems—keeping bad actors out while keeping things running smoothly.

